ARE YOUR SYSTEMS AND DATA PROTECTED AGAINST CYBERATTACKS AND UNAUTHORIZED ACCESS?
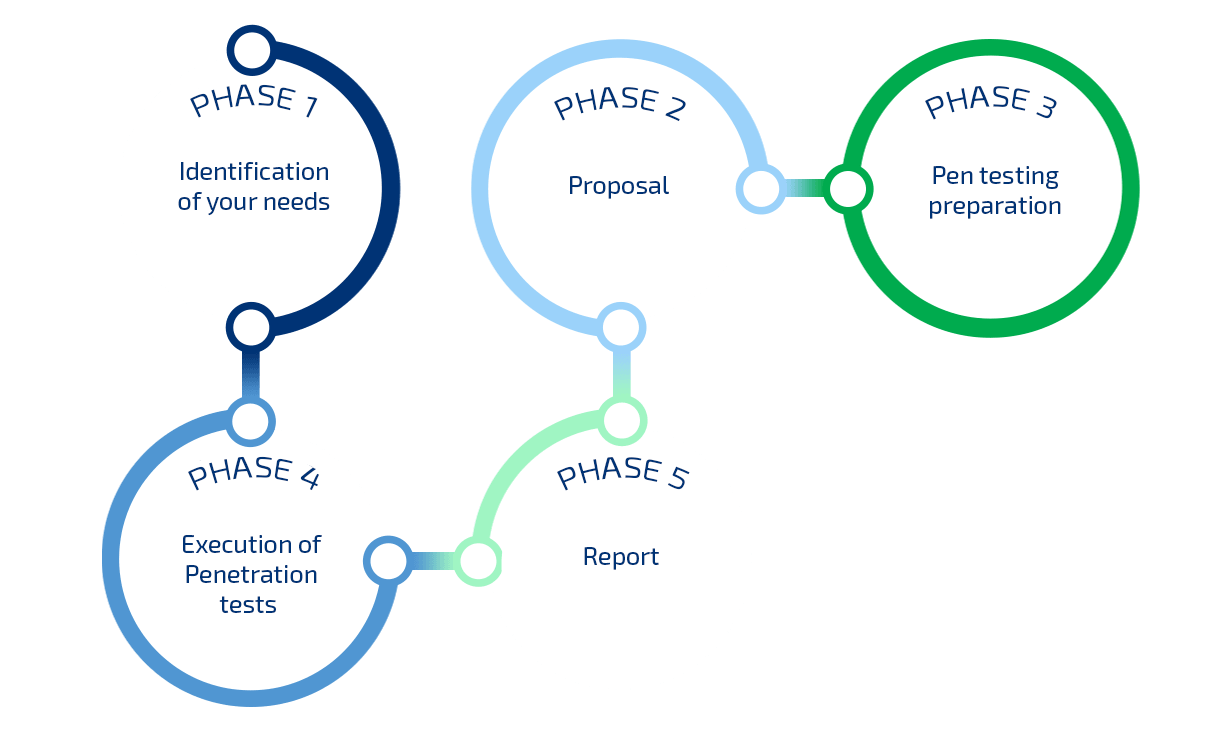
Check if your systems are vulnerable by conducting Penetration Tests!
Keep your systems secure in the current dynamically changing IT environment
Identify, verify, and assess vulnerabilities specific to your IT environment
Prioritize cybersecurity plan according to the applicability and impact of threats to your organization
Include expert intelligence, ensuring the accuracy of the results and analysis of their significance for the organization

 Български
Български